SAIC is built for
your industry
A versatile architecture that adapts to the cryptographic requirements of any sector — from securing SOC operations to protecting subscriber communications to enabling private AI.
Transform your SOC into a
next-generation security provider
SOCs emerged as the de-facto insurance policy for enterprise security. But the modern SOC needs to go beyond threat monitoring — it needs to be a proactive business security solutions provider. ScipherX SAIC was architected with the SOC model in mind.
The architectural similarities between SAIC and SOC infrastructure create a hand-in-glove fit: one point of distribution, revocation, and charging. SAIC augments your existing SOC capabilities with encryption as a service — a category your clients are urgently demanding.
The Opportunity
What SAIC Delivers to SOCs
The Three Zeroes for Telcos
Zero CapEx Required
No upfront capital expenditure. Pricing is based on subscriber adoption — fully aligned with your revenue model. Deploy ScryptX products to your subscriber base without infrastructure investment.
Zero Liability Architecture
Keys for secure email and encrypted data storage are never stored by the telecom operator — or by ScipherX. This eliminates operator liability for key compromise in the event of a security incident.
Zero Friction Implementation
Turnkey solution. No complex integrations, no staff retraining, no disruption to existing infrastructure. ScryptX applications work alongside current email and storage solutions as an additional security layer.
Secure your subscribers.
Build new revenue streams.
Credential phishing, ransomware, and identity theft are driving growing demand from subscribers for enhanced communication security. Current solutions require complex integrations and steep learning curves. ScryptX changes that.
ScryptX Mail and Encryptor — powered by SAIC — integrate seamlessly with your subscribers' existing email and storage habits. No switching. No migration. Post-quantum encrypted communications in days, not months.
Telco partners have two deployment paths: licence ScryptX Mail and Encryptor directly under your own brand — white-labelled with your logo and subscriber management — or integrate SAIC directly via API to build your own secure communications products. Both paths carry zero operator liability for key compromise, because keys are never stored by the operator or by ScipherX.
The Opportunity for Telcos
- Increase subscriber stickiness with value-added security services
- Generate recurring revenue from existing subscriber base
- Reduce churn by building trust and enhancing privacy
- Offer white-labelled secure communications under your brand
- Expand into enterprise security services market
End-to-end data governance at enterprise scale
From individual emails to vast data lakes, SAIC provides granular cryptographic control over every piece of data across your organisation — with a single dashboard.
Data Encryption
Encrypt emails, files, databases, data lakes, and cloud workloads with a single platform. Post-quantum resistant from day one.
Access Control / RBAC
Fine-grained role-based access control with constraints. Set who can access what, from where, for how long, and how many times.
Dynamic Tag-Based Control
Tag datasets and apply policies automatically based on data classification — PII, PHI, payment data, confidential. Policies travel with the data.
Compliance Automation
Automated evidence collection for GDPR, HIPAA, SOC 2, PCI-DSS, and CCPA. Tamper-proof audit trails. Exportable compliance reports.
Private AI Training
Train AI and ML models on sensitive data without the training service ever seeing plaintext. Federated learning with cryptographic confidentiality.
Key Request Visualisation
Pan-regional, multi-dimensional visualisation that keeps complex access activity legible — patterns and outliers surface before they become incidents.
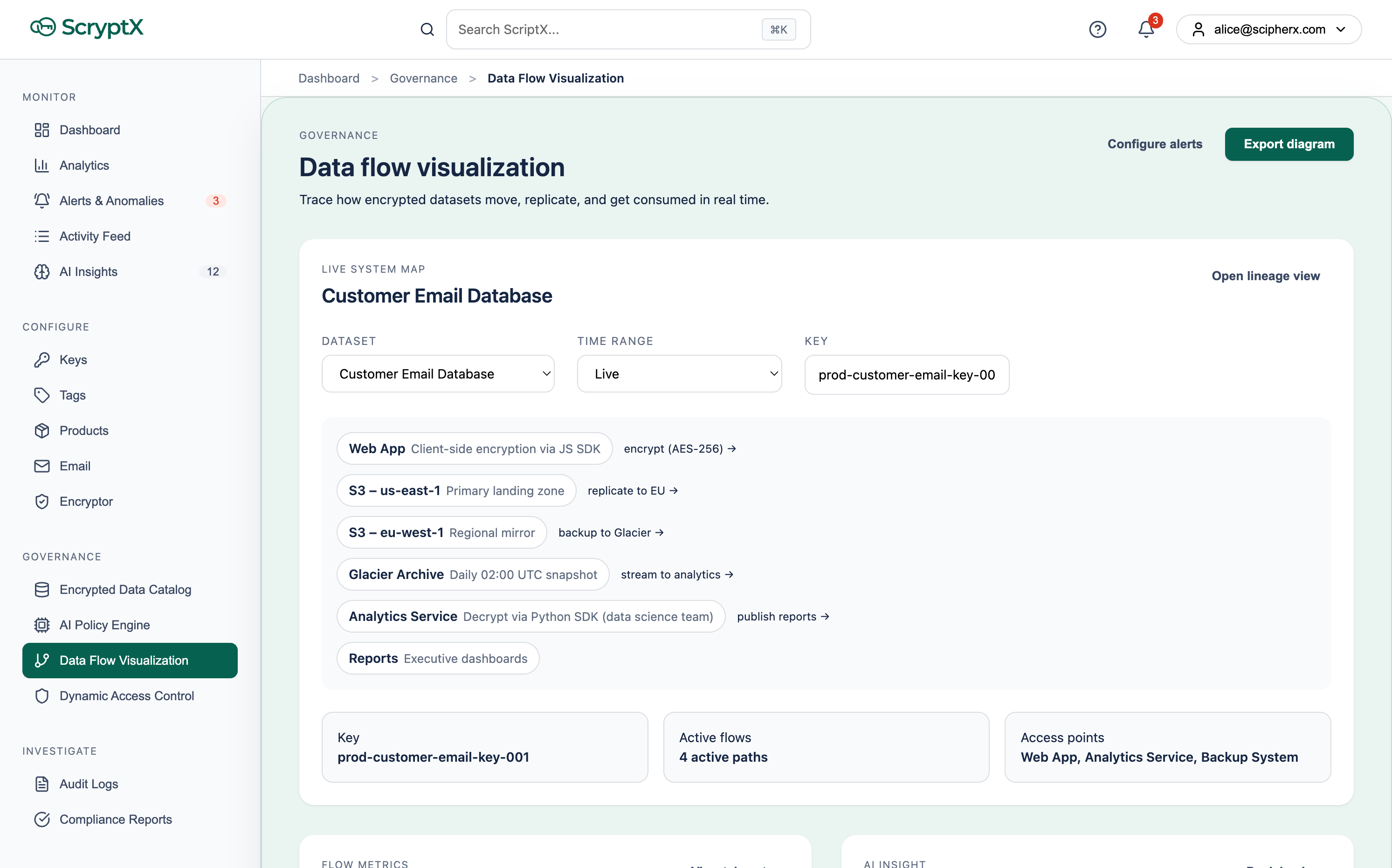
Pan-regional views and the dimensions your teams track every day
Security beyond the desktop
SAIC's lightweight, standards-based architecture is purpose-built to scale from smartphones to IoT sensors, electric vehicles to maritime vessels, smart buildings to developer programmes.
IoT Devices
Protect IoT sensor data and device communications with post-quantum encryption. Policy-based access control travels with every data packet. DeviceUser type supports non-human endpoints natively.
Smart Mobility & EVs
Secure vehicle-to-vehicle and vehicle-to-infrastructure communications. Policy-based control for infotainment, diagnostics, navigation, and event data. End users share data privately and securely.
Maritime Transport
Secure ship-to-shore communications and inter-vessel data sharing. Policy-based control for cargo monitoring, navigation, regulatory compliance, and safety systems across the entire supply chain.
Critical Infrastructure
Protect industrial control systems, smart grids, and critical national infrastructure with post-quantum encryption. Policy-based access control ensures only authorised systems and operators can access sensitive operational data — even in complex, multi-stakeholder environments.
Developer Programme
~8 million iOS and Android developers making an average of 5 apps each represents 40 million potential SAIC-powered applications. Our Developer Programme makes it simple to embed post-quantum security into any application.
Ready to partner with ScipherX?
Whether you're a SOC looking to expand your service portfolio, a Telco building subscriber loyalty, or an enterprise securing your data at scale — we're ready to build together.