The SAIC Platform
A standards-based, post-quantum resistant cryptographic key management protocol with fine-grained AI policy control. The same enforcement model applies everywhere your data moves. One platform for every use case — from emails to data lakes, IoT devices to cloud workloads.
Real-Time Monitoring
Your security command centre
A unified dashboard with real-time visibility into every encryption operation, AI-detected anomaly, and compliance signal — so teams can spot issues early and contain them before they spread.
Centralised Dashboard
Active keys, operation volumes, compliance scores, and anomalies — with drill-down by product, team, and data classification.
Severity-Prioritised Alerts
AI triages and escalates by severity (Critical / High / Medium). Routes to email, Slack, or PagerDuty with response tracking.
AI-Powered Recommendations
Surfaces keys to archive, policy gaps, and configuration fixes — each with impact and a suggested next step.
Platform Architecture
Two engines, one unified platform
SAIC combines a post-quantum cryptographic PaaS with an AI-driven policy PaaS, operating above the transport layer to protect applications and data at their foundational level — limiting blast radius when something goes wrong.
Cryptographic PaaS
Post-quantum resistant engine operating above the transport layer — securing applications and data at the foundational level. Built on NIST-approved standards from day one.
AI Policy PaaS
Distributed AI and machine learning engine providing policy-based malware prevention and privacy-enhanced federated learning.
Where SAIC Operates
ISO 7-Layer Model — unlike transport-layer encryption (TLS/SSL), SAIC protects data at rest, in transit, and in use
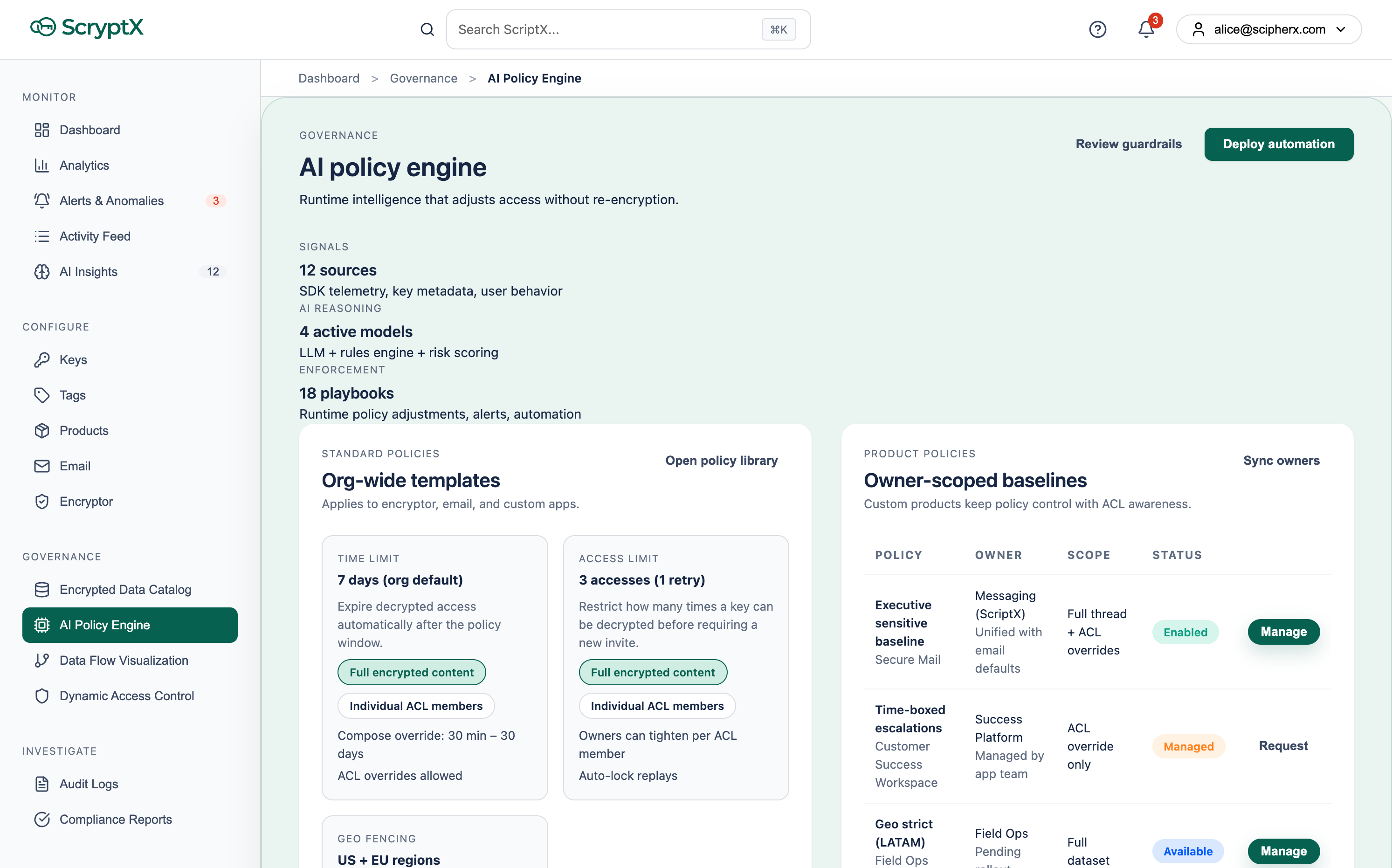
The SAIC AI Engine — live portal view
How SAIC is built
Cryptographic isolation
Each operation uses minimal key material — no global keys reused across contexts.
Revocable encryption
Withdraw access after data is shared — unlike static email attachments or file links.
Cryptographic agility
Swap algorithms as standards evolve — see our white papers for the architecture.
Breach containment
Security is not only confidentiality — the design limits how far a compromise can spread.
Channel-agnostic
One protection model across email, files, APIs, and internal workflows.
Decentralised Key Management
Zero keys stored on any server.
Ever.
SAIC isolates key material to each operation and context — no global keys reused across apps or tenants. The distributed architecture removes the single point of failure of traditional KMS: keys are computed on-demand and never persisted on any server.
Distributed Key Request Flow
RBAC & Policy Engine
Granular control at every level
SAIC implements Role-Based Access Control with a rich constraint system — including revocable encryption so access can be withdrawn after data is shared, unlike static attachments or shared links.
User Roles
Policy Constraints
Set expiry windows — 30 min to 30 days. After expiry, access is automatically revoked without re-encryption.
dec_time_not_after: 7d Restrict how many times a document can be decrypted. Prevent unlimited forwarding.
dec_max_calls: 3 Allow or deny decryption by region for residency and compliance.
dec_loc_allowed: UK, EU 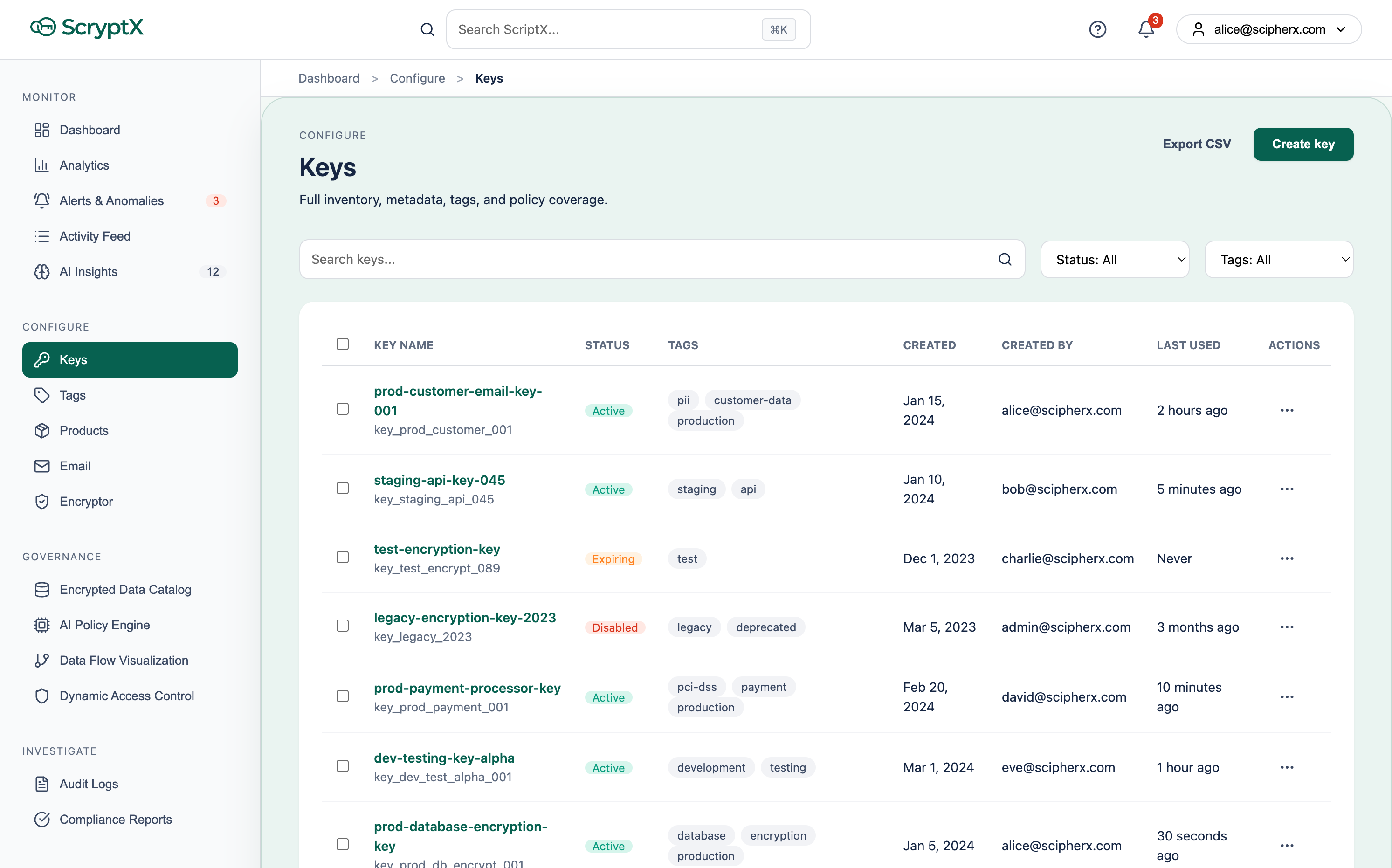
Key inventory with full tag-based policy coverage
Policies travel with the data, not just the platform.
Developer-First
3 lines of code.
Enterprise-grade security.
The SAIC API hides sophisticated backend interactions — key generation, encryption, secure transmission, and policy enforcement — behind an elegant interface. Backed by robust enterprise infrastructure designed to handle the most critical data protection challenges.
Supported Languages & Platforms
Using Claude, Cursor, or an AI coding assistant? → Explore SAIC MCP Access
import saic
# Initialise with 3 lines
client = saic.Client(api_key="your-key")
policy = client.policy(geo="UK,EU", expires="7d")
encrypted = client.encrypt(data, policy=policy)
# Decrypt — client-side only
# Server never sees plaintext
plaintext = client.decrypt(encrypted)Minimal Code, Maximum Security — Fast, Scalable, and Secure
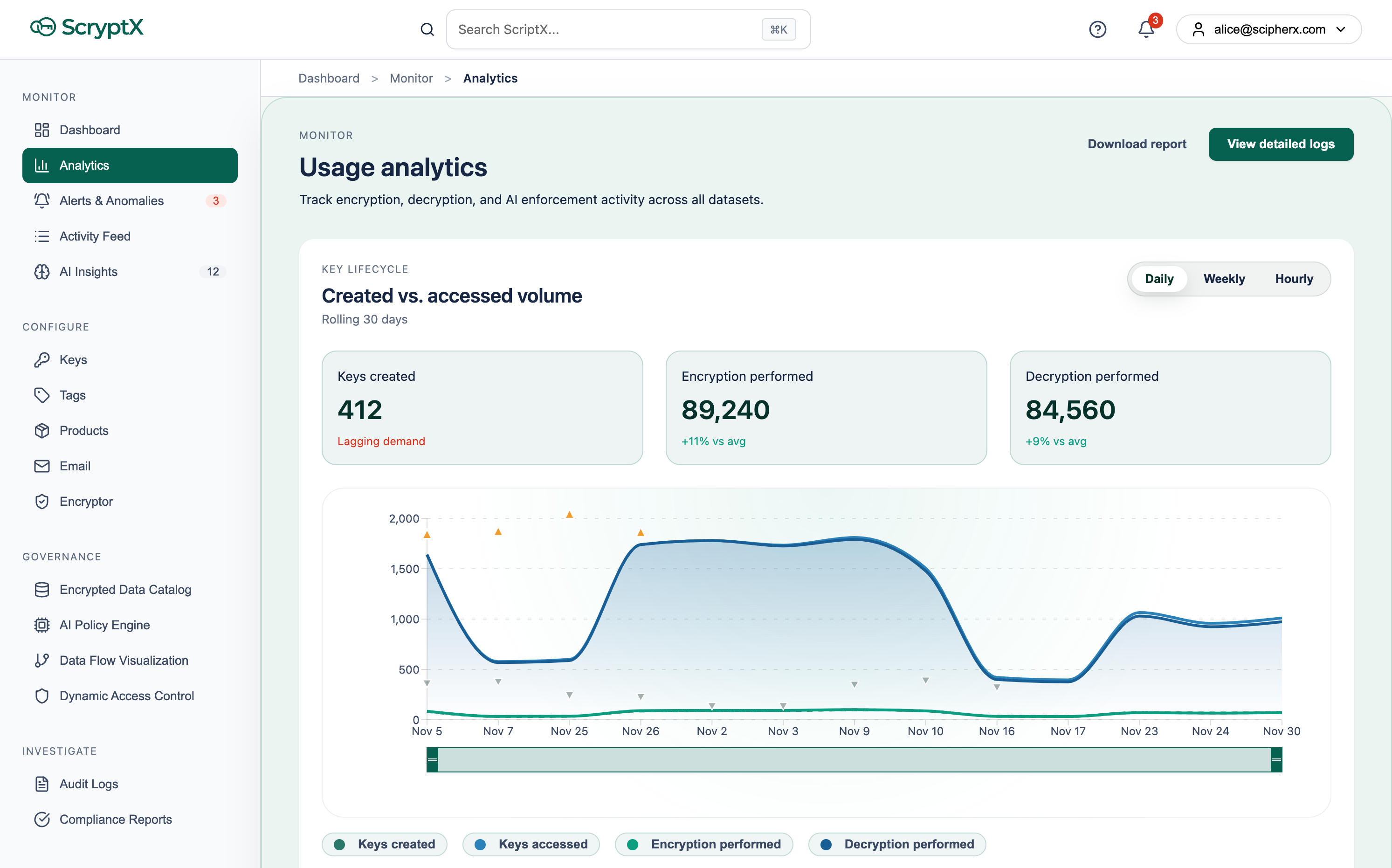
Real-time usage analytics — track every encryption operation across all datasets
Integration & Compliance
Designed for your existing ecosystem
ScipherX SAIC integrates seamlessly with your existing IT infrastructure — no rip-and-replace, no complex migrations.
Zero-Friction Integration
- Connects to existing MSSP
- Integrates with orchestration tools (Zapier, etc.)
- No capital expenditure required
- Subscriber-based pricing model
Compliance Built-In
- GDPR compliance with geo-fencing
- HIPAA-ready audit trails
- ISO/IEC 27001 aligned
- SOC 2 controls automated
Enterprise Scale
- Internet-scale population support
- Franchise model for global deployment
- Multi-tenant B2B & B2C
- White-label support
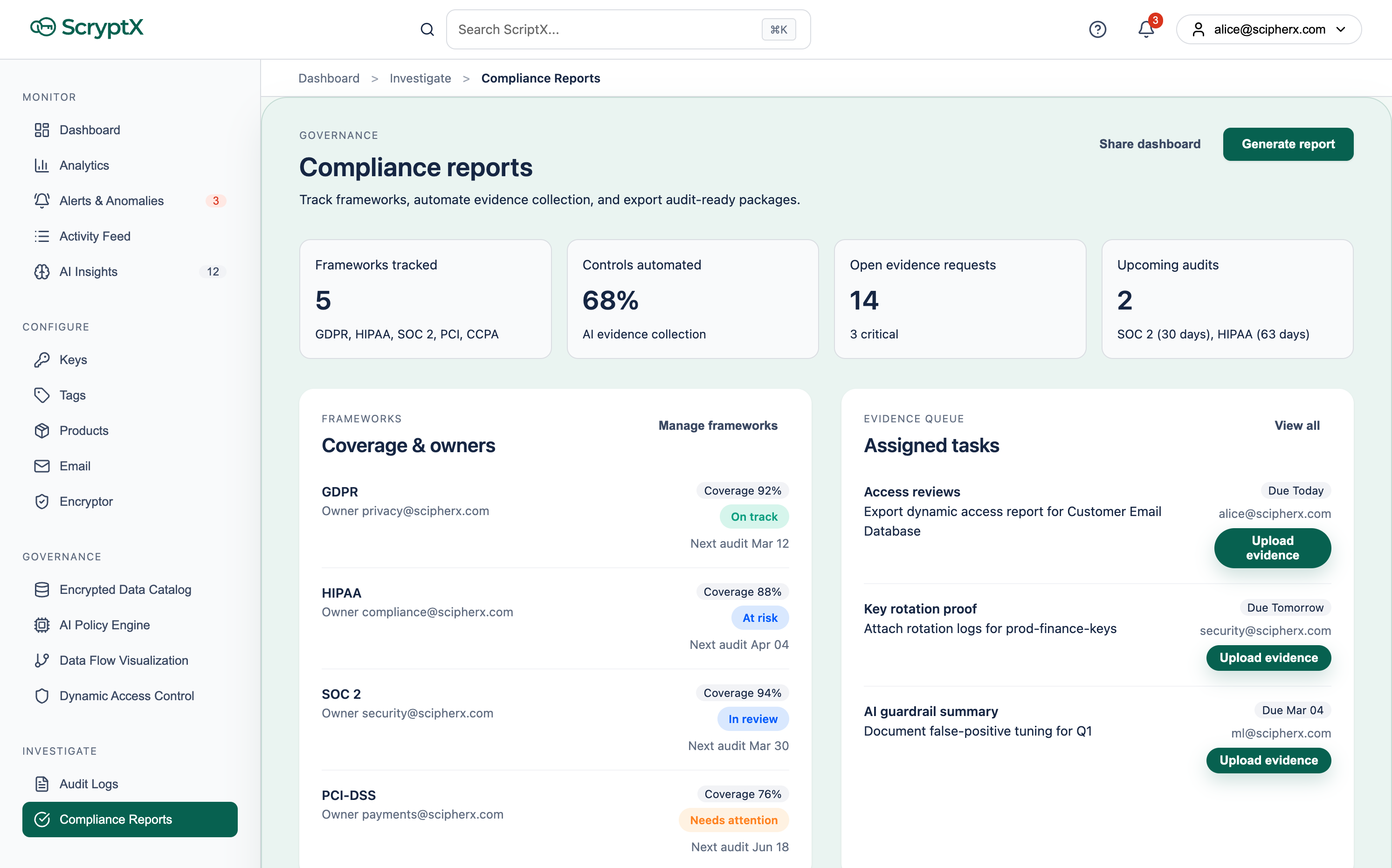
Automated compliance tracking across GDPR, HIPAA, SOC 2, and PCI-DSS
Data Governance
Visibility into all your encrypted data.
Without ever seeing it.
SAIC's Governance layer gives your security team real-time oversight of every encrypted dataset across the organisation — access patterns, data lineage, risk signals, and dynamic controls — all without the platform ever processing plaintext.
AI Engine
Runtime policy adjustments, anomaly alerts, and enforcement — without re-encryption. The same engine can orchestrate approved client-side AI processing on your data (for example, summarisation) while keeping plaintext off ScipherX servers.
Policy & client-side AIKey Request Visualisation
Pan-regional, multi-dimensional visualisation that keeps complex access activity legible — patterns and outliers surface before they become incidents.
Governance viewDynamic Access Control
Revoke or grant access to encrypted data instantly — without re-encrypting. Shrinks the active access footprint when risk changes. Just-in-time access for privileged operations; AI recommends and operators approve or auto-enforce.
Instant revocationAudit & Compliance
Tamper-proof. Always audit-ready.
Immutable audit logs with real-time streaming, AI-powered event correlation, and built-in compliance reporting for every major regulatory framework.
Audit Log Capabilities
- Immutable, tamper-proof audit trail
- Stream and filter by user, operation, key, IP, and location
- AI-assisted correlation for faster investigations
- SIEM export to your security analytics stack
- Structured evidence for investigations and audits
Compliance coverage
SAIC is built to support compliance-oriented workflows: structured evidence, access lineage, and exportable reports your assurance teams can map to the obligations that apply to you. You remain responsible for interpretation, scope, and attestation — the platform supplies the operational record.
Examples of regimes the product surface is designed around
Generate audit-ready documentation (for example PDF or DOCX) and stream events into your existing GRC or SIEM stack.
Read the research behind SAIC
Our technical white papers detail the cryptographic architecture, RBAC model, AI engine, and how cryptographic agility works as standards evolve — all on the SAIC platform.
Ready to build on SAIC?
Get API access and start protecting your application in minutes. Our team of cryptography experts will guide your integration.